By mining, you can earn cryptocurrency without having to put down money for it. That said, you certainly don't have to be a miner to own crypto. You can also buy crypto using fiat currency (USD, EUR, JPY, etc); you can trade it on an exchange like Bitstamp using other crypto (example: Using Ethereum or NEO to buy Bitcoin); you even can earn it by playing video games or by publishing blogposts on platforms that pay its users in crypto. An example of the latter is Steemit, which is kind of like Medium except that users can reward bloggers by paying them in a proprietary cryptocurrency called Steem. Steem can then be traded elsewhere for Bitcoin.
In addition to lining the pockets of miners, mining serves a second and vital purpose: It is the only way to release new cryptocurrency into circulation. In other words, miners are basically "minting" currency. For example, as of the time of writing this piece, there were about 16 million Bitcoin in circulation. Aside from the coins minted via the genesis block (the very first block created by Bitcoin founder Satoshi Nakamoto himself), every single one of those Bitcoin came into being because of miners. In the absence of miners, Bitcoin would still exist and be usable, but there would never be any additional Bitcoin. There will come a time when Bitcoin mining ends; per the Bitcoin Protocol, the number of Bitcoin will be capped at 21 million.
How much can a miner earn from mining Bitcoin?
Bitcoin are mined in units called "blocks." As of the time of writing, the reward for completing a block is 12.5 Bitcoin. At today's price of about $5000 per Bitcoin, this means you'd earn (12.5 x 5000)=$62,500.
When Bitcoin was first mined in 2009, mining one block would earn you 50 BTC. In 2012, this was halved to 25 BTC. in 2016, this was halved to the current level of 12.5 BTC. In 2020 or so, the reward size will be halved again to 6.25 BTC.
If you want to keep track of precisely when these halvings will occur, you can consult the Bitcoin Clock, which updates this information in real time.
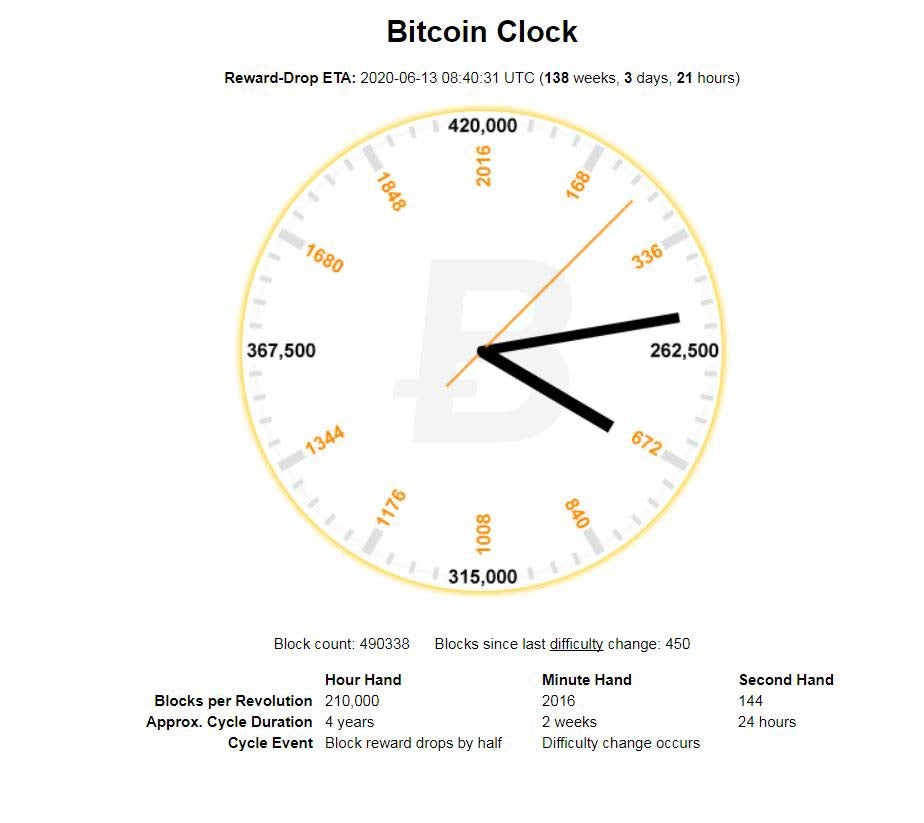
(Source: Bitcoinclock.com)
How many blocks have been mined so far?
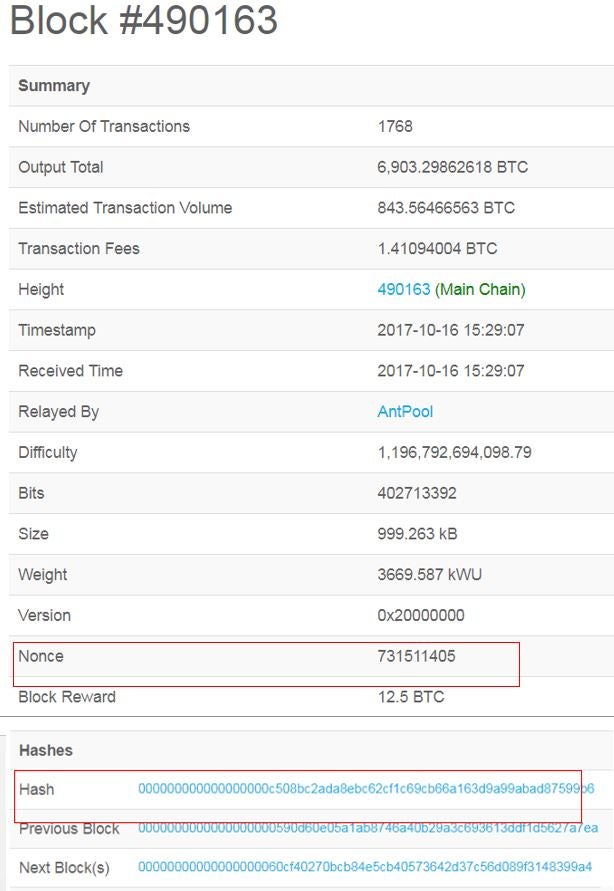
A number of sites, including Blockchain.info, will give you that information in real time. At the time of writing, we are at block # 490163.
What are miners doing that's so important that they get free Bitcoin?
Miners are getting paid for their work as auditors. They are doing the work of verifying previous Bitcoin transactions. This convention is meant to keep Bitcoin users honest, and was conceived by Bitcoin's founder, Satoshi Nakamoto. By verifying transactions, miners are helping to prevent the "double-spending problem."
Double spending means, as the name suggests, that a Bitcoin user is illicitly spending the same money twice. With physical currency, this isn't an issue: Once you hand someone a greenback $20 bill to buy a bottle of vodka, you no longer have it, so there's no danger you could use that same $20 to buy lotto tickets next door. With digital currency, however, as the Investopedia dictionary explains, "there is a risk that the holder could make a copy of the digital token and send it to a merchant or another party while retaining the original."
Let's say you had one legit $20 and one really good photocopy of that same $20. If someone were to try to spend both the real bill and the fake one, someone who took the trouble of looking at both of the bills' serial numbers would see that they were the same number, and thus one of them had to be false. What a Bitcoin miner does is analogous to that--they check transactions to make sure that users have not illegitimately tried to spend the same Bitcoin twice. This isn't a perfect analogy--we'll explain in more detail below.
Once a miner has verified 1 MB (megabyte) worth of Bitcoin transactions, they are eligible to win the 12.5 BTC. The 1 MB limit was set by Satoshi Nakamoto, and is a matter of controversy, as some miners believe the block size should be increased to accommodate more data.
Note that I said that verifying 1 MB worth of transactions makes a miner eligible to earn Bitcoin--not everyone who verifies transactions will get paid out.
1MB of transactions can theoretically be as small as 1 transaction (though this is not at all common) or several thousand. It depends on how much data the transactions take up.
So after all that work of verifying transactions, I might still not get any Bitcoin for it?
That is correct.
In order to earn Bitcoin, you need to meet two conditions. One is a matter of effort, one is a matter of luck.
1) You have to verify ~1MB worth of transactions. This is the easy part.
2) You have to be the first miner to arrive at the right answer to a numeric problem. This process is also known as a proof of work.
What do you mean, "the right answer to a numeric problem"?
The good news: No advanced math or computation is involved. You may have heard that miners are solving difficult mathematical problems--that's not true at all. What they're actually doing is trying to be the first miner to come up with a 64-digit hexadecimal number (a "hash") that is less than or equal to the target hash. It's basically guess work.
The bad news: Because it's guesswork, you need a lot of computing power in order to get there first. To mine successfully, you need to have a high "hash rate," which is measured in terms of megahashes per second (MH/s), gigahashes per second (GH/s), and terahashes per second (TH/s).
That is a great many hashes.
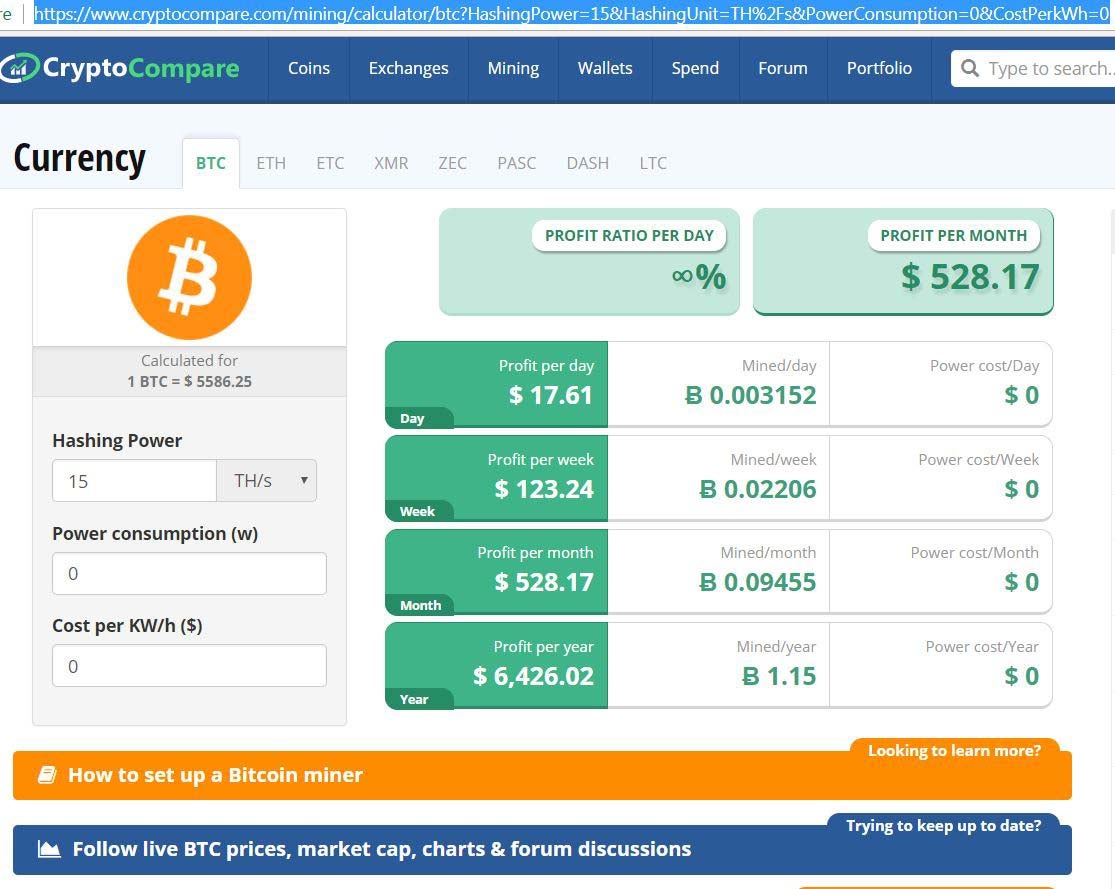
If you want to estimate how much Bitcoin you could mine with your mining rig's hash rate, the site Cryptocompare offers a helpful calculator.
What equipment do I need to mine?
Either a GPU (graphics processing unit) miner or an application-specific integrated circuit (ASIC) miner. These can run from $500 to the tens of thousands. Some miners--particularly Ethereum miners--buy individual graphics cards as a low-cost way to cobble together mining operations. The photo below is a makeshift, home-made mining machine. The graphics cards are those rectangular blocks with whirring circles. Note the sandwich twist-ties holding the graphics cards to the metal pole. This is probably not the most efficient way to mine, and as you can guess, many miners are in it as much for the fun and challenge as for the money.
The ELI5 ("Explain It Like I'm Five") version of what Bitcoin miners do
Example: I tell three friends that I'm thinking of a number between 1 and 100, and I write that number on a piece of paper and seal it in an envelope. My friends don't have to guess the exact number, they just have to be the first person to guess any number that is less than or equal to the number I am thinking of. And there is no limit to how many guesses they get.
Let's say I'm thinking of the number 19. If Friend A guesses 21, they lose because 21>19. If Friend B guesses 16 and Friend C guesses 12, then they've both theoretically arrived at viable answers, because 16<19 12="" 19.="" and="" answer="" b="" closer="" credit="" even="" extra="" for="" friend="" is="" no="" of="" p="" s="" target="" the="" there="" though="" to="" was="">


If B and C both answer simultaneously, then the ELI5 analogy breaks down.
In Bitcoin terms, simultaneous answers occur frequently, but at the end of the day there can only be one winning answer. When multiple simultaneous answers are presented that are equal to or less than the target number, the Bitcoin network will decide by a simple majority--51%--which miner to honour. Typically, it is the miner who has done the most work, i.e. verifies the most transactions. The losing block then becomes an "orphan block."
Now imagine that I pose the "guess what number I'm thinking of" question, but I'm not asking just three friends, and I'm not thinking of a number between 1 and 100. Rather, I'm asking millions of would-be miners and I'm thinking of a 64-digit hexadecimal number. Now you see that it's going to be extremely hard to guess the right answer.
What the hell is a "64-digit hexadecimal number"?
Well, here is one:
0000000000000000057fcc708cf0130d95e27c5819203e9f967ac56e4df598ee
The number above has 64 digits. Easy enough to understand so far. As you probably noticed, that number consists not just of numbers, but also letters of the alphabet. Why is that?
In order to understand what these letters are doing in the middle of numbers, let's unpack the word "hexadecimal."
As you know, we use the "decimal" system, which means it is base 10. This in turn means that every digit has 10 possibilities, 0-9. I will be rather alarmed if these do not look familiar to you:
0 1 2 3 4 5 6 7 8 9
"Hexadecimal," on the other hand, means base 16, as "hex" is derived from the Greek word for 6 and "deca" is derived from the Greek word for 10. In a hexadecimal system, each digit has 16 possibilities. But our numeric system only offers 10 ways of representing numbers (0-9). That's why you have to stick letters in, specifically letters a, b, c, d, e, and f. In a hexadecimal system, these are the values of each digit:
| Hexadecimal figure | Decimal equivalent |
| 0 | 0 |
| 1 | 1 |
| 2 | 2 |
| 3 | 3 |
| 4 | 4 |
| 5 | 5 |
| 6 | 6 |
| 7 | 7 |
| 8 | 8 |
| 9 | 9 |
| a | 10 |
| b | 11 |
| c | 12 |
| d | 13 |
| e | 14 |
| f | 15 |
The above chart is just for background. If you are mining Bitcoin, you do not need to calculate the total value of that 64-digit number (the hash). I repeat: You do not need to calculate the total value of a hash.
Thanks a lot. So what do "64-digit hexadecimal numbers" have to do with Bitcoin mining?
Remember that ELI5 analogy, where I wrote the number 19 on a piece of paper and put it in a sealed envelope?
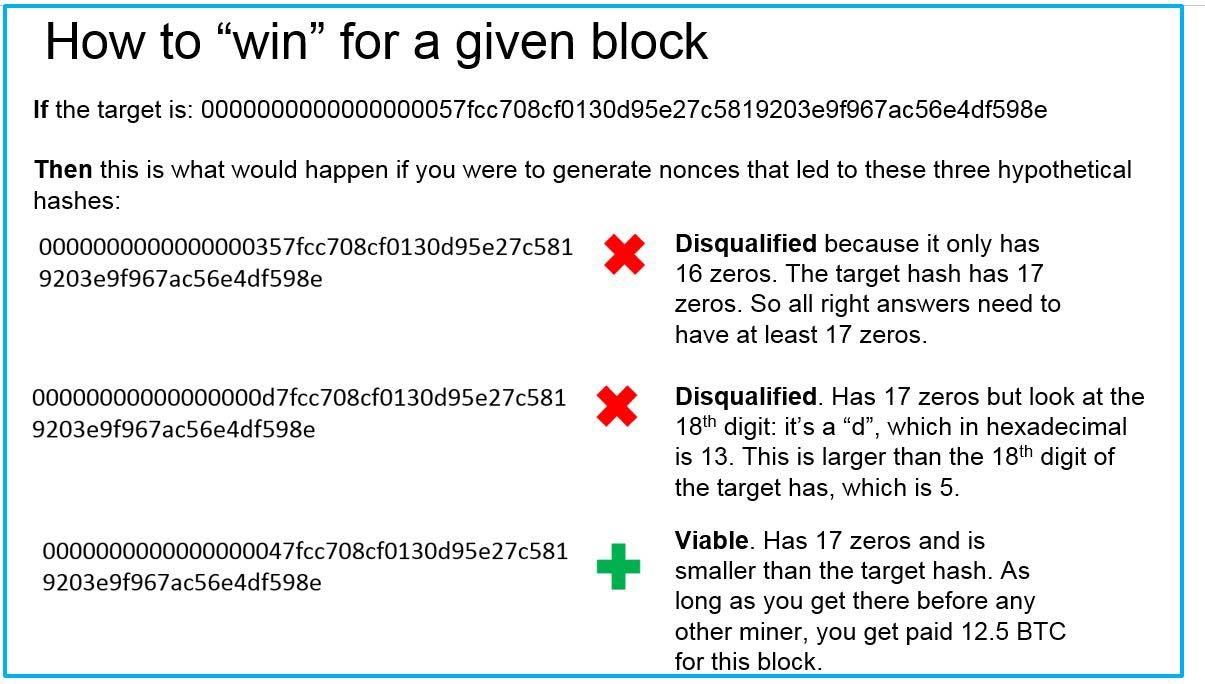
In Bitcoin mining terms, that metaphorical undisclosed number in the envelope is called the target hash.
What miners are doing with those huge computers and dozens of cooling fans is guessing at the target hash. Miners make these guesses by randomly generating as many "nonces" as possible, as fast as possible. A nonce is short for "number only used once," and the nonce is the key to generating these 64-bit hexadecimal numbers I keep talking about. In Bitcoin mining, a nonce is 32 bits in size--much smaller than the hash, which is 256 bits. The first miner whose nonce generates a hash that is less than or equal to the target hash is awarded credit for completing that block, and is awarded the spoils of 12.5 BTC.
In theory you could achieve the same goal by rolling a 16-sided die 64 times to arrive at random numbers, but why on earth would you want to do that?
The screenshot below, taken from the site Blockchain.info, might help you put all this information together at a glance. You are looking at a summary of everything that happened when block #490163 was mined. The nonce that generated the "winning" hash was 731511405. The target hash is shown on top. The term "Relayed by: Antpool" refers to the fact that this particular block was completed by AntPool, one of the more successful mining pools. As you see here, their contribution to the Bitcoin community is that they confirmed 1768 transactions for this block. If you really want to see all 1768 of those transactions for this block, go to this page and scroll down to the heading "Transactions."
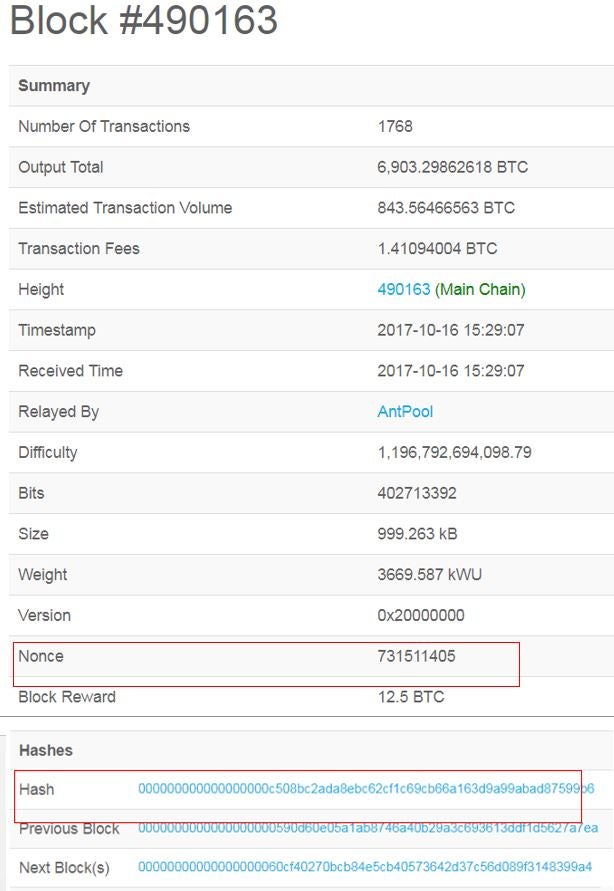
(source : Blockchain.info)
OK so how do I guess at the target hash?
All target hashes begin with zeros--at least eight zeros, and up to 63 zeros.
There is no minimum target, but there is a maximum target set by the Bitcoin Protocol. No target can be greater than this number:
00000000ffff0000000000000000000000000000000000000000000000000000
Here are some examples of randomized hashes and the criteria for whether they will lead to success for the miner:
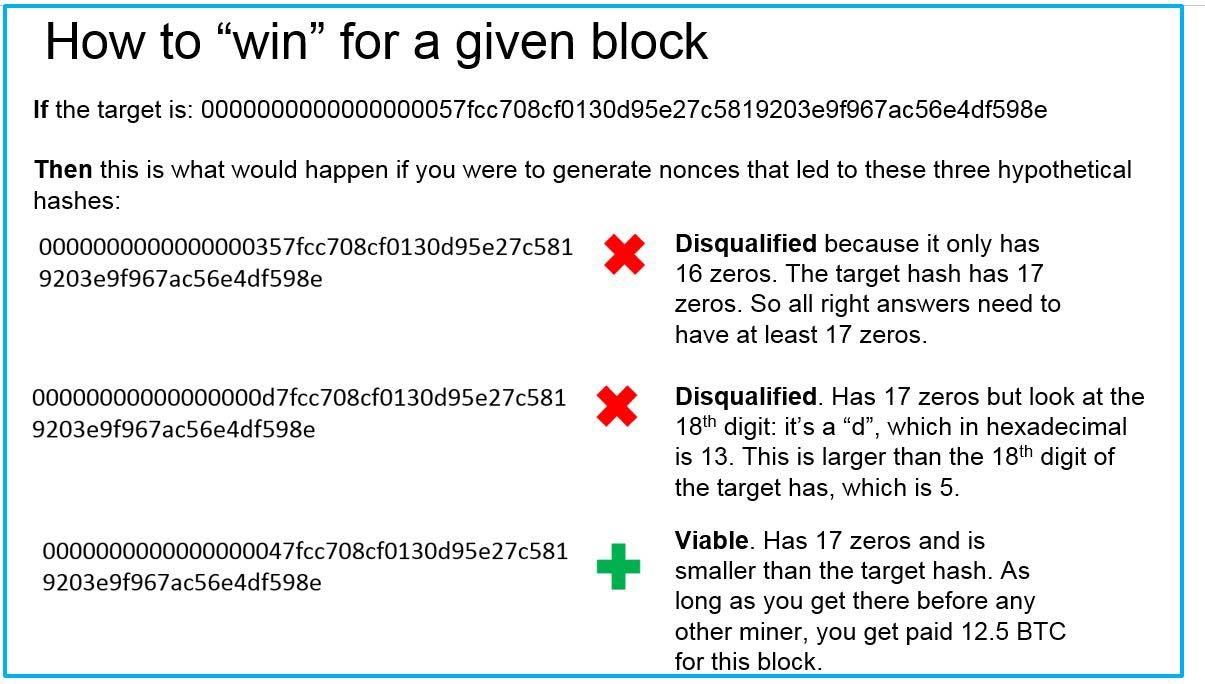
(Note: These are made-up hashes)
How do I maximize my chances of guessing the target hash before anyone else does?
You'd have to get a fast mining rig or, more realistically, join a mining pool--a group of miners who combine their computing power and split the mined bitcoin. Mining pools are comparable to those Powerball clubs whose members buy lottery tickets en masse and agree to share any winnings. A disproportionately large number of blocks are mined by pools rather than by individual miners.
In other words, it's literally just a numbers game. You cannot guess the pattern or make a prediction based on previous target hashes. The difficulty level of the most recent block at the time of writing is 1,196,792,694,099, i.e. the chance of any given nonce producing a hash below the target is 1 in 1,196,792,694,099--less than 1 in a trillion.
How do I decide whether Bitcoin will be profitable for me?
The aforementioned site Cryptocompare offers a helpful calculator that allows you to plug in numbers such as your hash speed, electricity costs etc. to estimate the costs and benefits. 
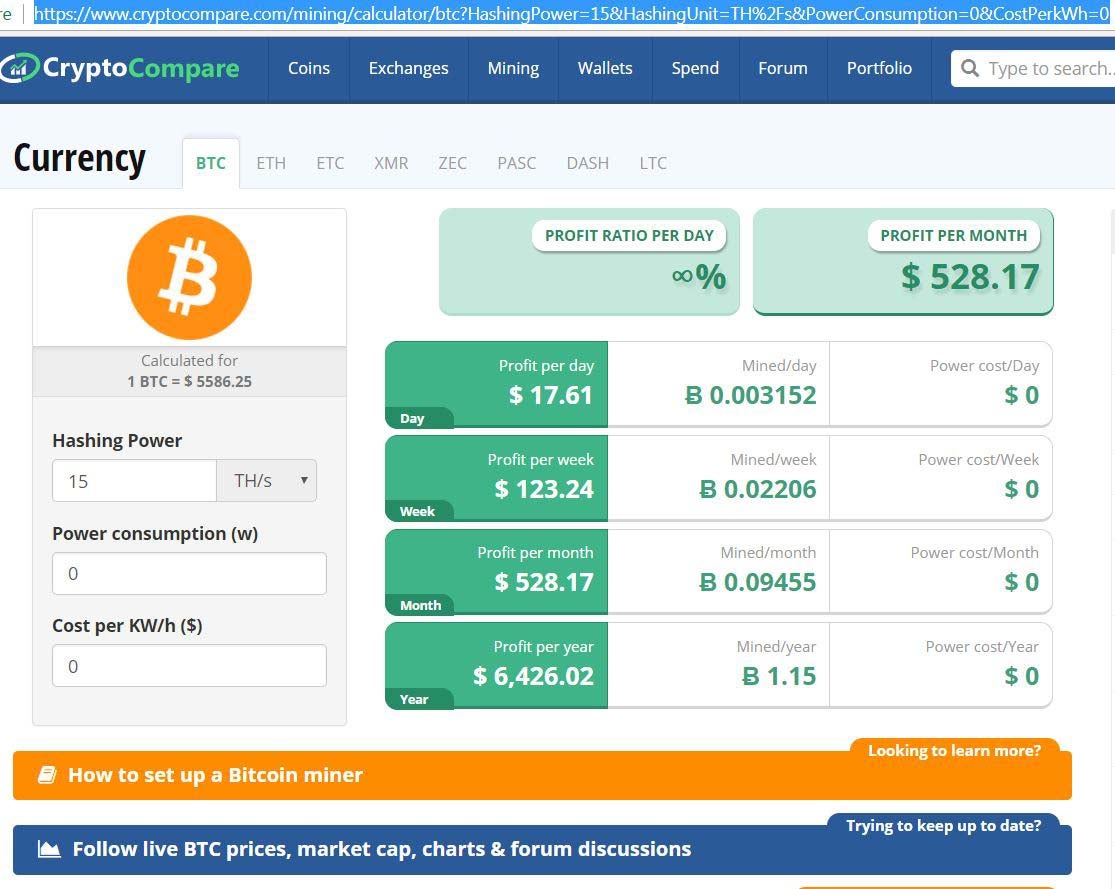
(Source: Cryptocompare)
I've done the math. Forget mining. Is there a less onerous way to profit from the Crypto boom?
Sure. As discussed, the easiest way to acquire Bitcoin is to buy it on an exchange like Coinbase.com. Alternately, you can always leverage the "pickaxe strategy". This is based on the old saw that during the 1848 California gold rush, the smart investment was not to pan for gold, but rather to make the pickaxes used for mining. Or, to put it in modern terms, invest in the companies that manufacture those pickaxes. In a crypto context, the pickaxe equivalent would be a company that manufactures equpiment used for Bitcoin mining. You can look into companies that make ASICs miners or GPU miners.
Companies that manufacture these products include AMD and Nvidia.
Comments
Post a Comment
share your thoughts ....